Tag: Workflows
-
OIG Access Requests and Workflows – Checking SoD In An Access Request
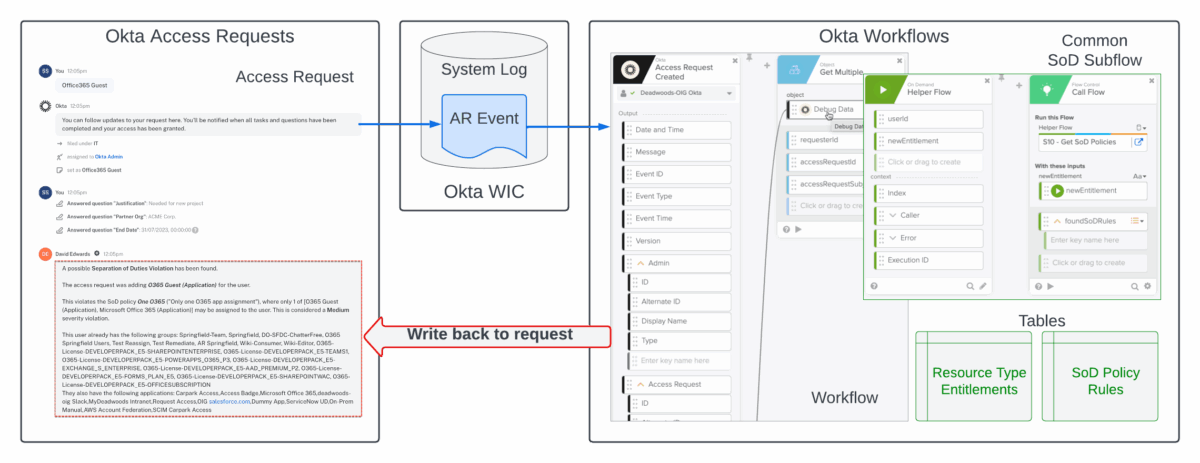
This article looks at a new approach you could use to perform Separation of Duties (SoD) checking from Okta Access Requests using Okta Workflows. It shows two approaches you could take to get SoD analysis into the request a soon as it’s raised so that the reviewer has the information at hand before approving the…
-
OIG Access Requests – Posting Additional Information into a Request
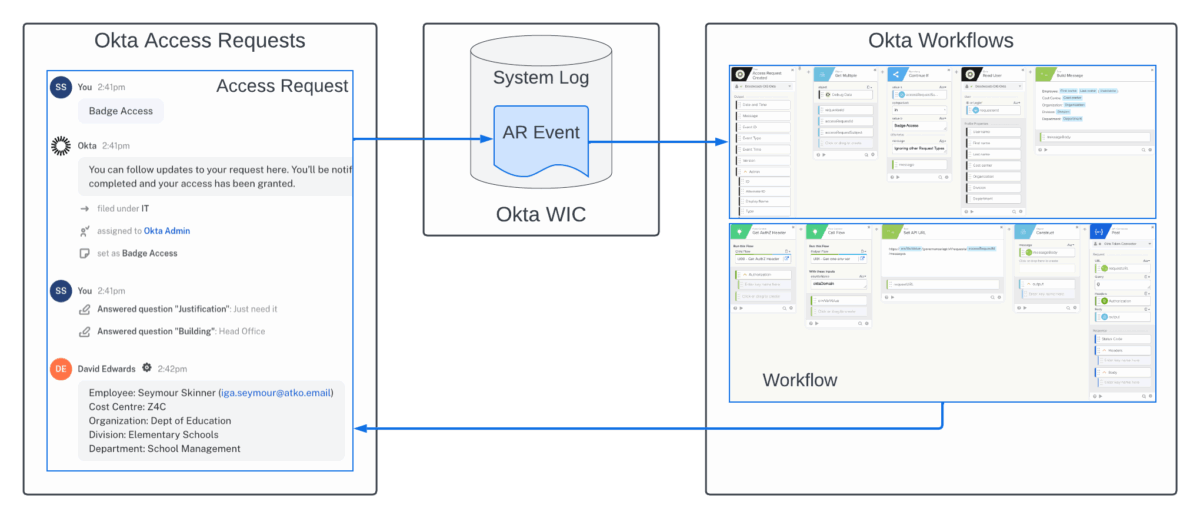
This article looks at a recent addition to the Okta Identity Governance (OIG) Access Request API that allows updating of in-flight access requests and can be used to add additional data to help reviewers review requests. Note that the OIG APIs are still in beta but can be used against preview and production Okta orgs.…
-
OIG Access Requests – Calling an Okta Workflow from Within a Request Type
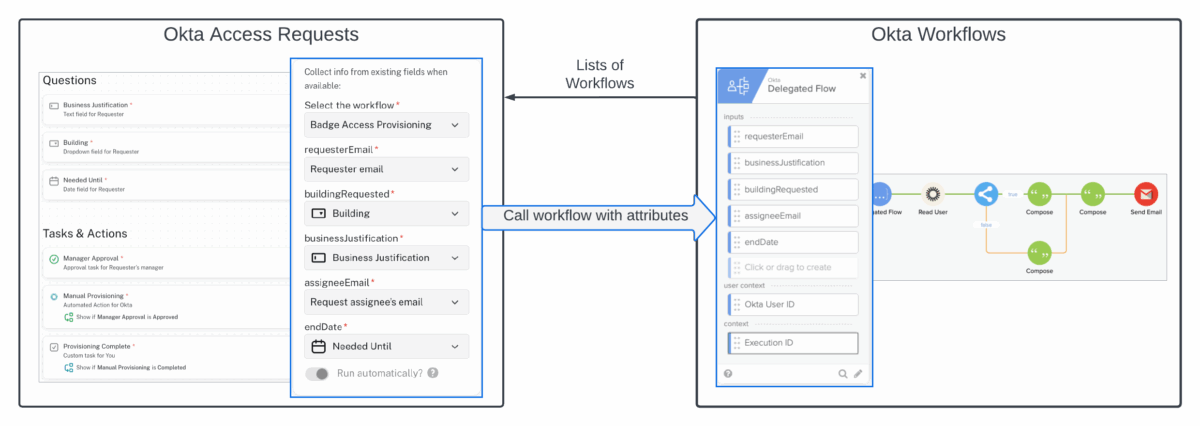
For some time there has been the ability to trigger a workflow in Okta Workflows from a request flow in Okta Access Requests via events written to the Okta System Log. Events were created for a request being initiated and being closed. But this approach has some limitations, such as a lot of processing within…
-
Understanding AWS IAM and Integrating with Okta and Workflows
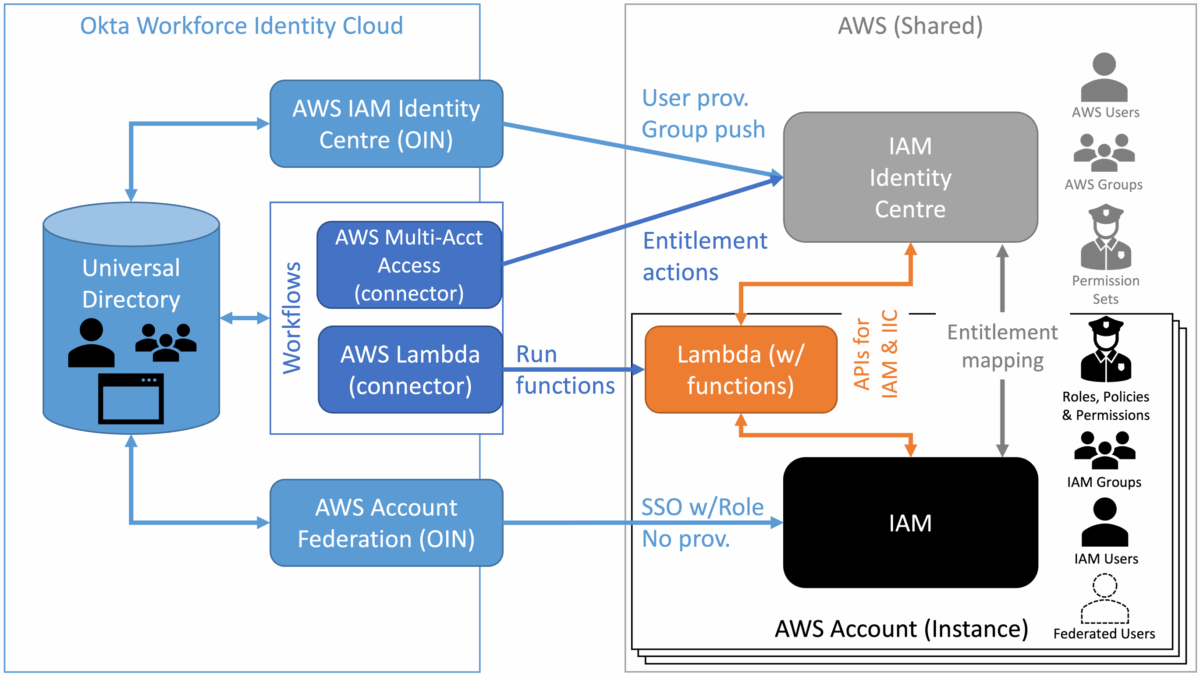
I’ve been looking into application entitlements and the Amazon Web Services (AWS) users, groups and entitlements has perplexed me for some time. I’ve had the opportunity to explore it, try to understand it and build some integration between Okta Workforce Identity Cloud (via Okta Workflows). This post is a summary of my findings. AWS and…
-
Okta Identity Governance and/or Service Now – Architectural Patterns
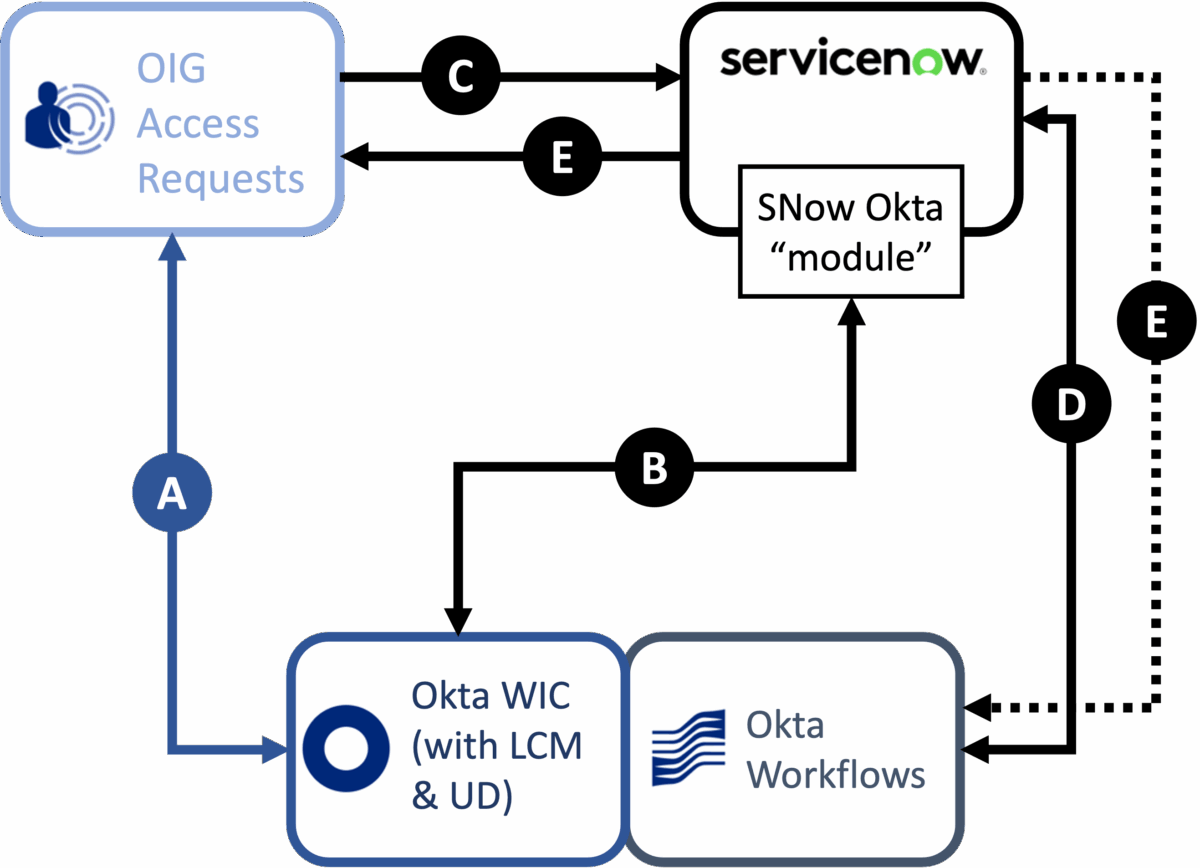
Most organisations have some ITSM or service request tool, and ServiceNow is the most common. So it’s understandable that any conversation about Okta Identity Governance, particularly access requests, will involve comparison with ServiceNow or integration patterns for both products. How do you approach an access request solution? Which product is going to meet your needs…
-
Risk-Based Application Certification in OIG
If you were at Oktane22, or have listened to the Oktane22 roadmap sessions, you will know risk and use of risk signals is a key focus for Okta going forward. This includes leveraging risk in Okta Identity Governance (OIG), to help make access requests and access certification more effective. But can you leverage risk today?…
-
Logging a ServiceNow Request via Workflows from OIG Access Requests
A common ask for Okta Identity Governance is to be able to log at ticket in a service desk tool, like ServiceNow, for manual provisioning activities after following an approval process in Access Requests. This article explores one approach to this using OIG Access Request events in the Okta System Log, Event Hooks and Okta…
-
Reassigning Managers for an Access Certification Campaign
A common requirement for Identity Governance and Administration (IGA) controls is for reassignment when a reviewer, like a manager, goes on leave. Okta Identity Governance (OIG) currently supports manual reassignment of access certification reviews by an administrator or by the reviewer themselves. But what about automatic reassignment based on a change to the user profile,…
-
OIG – Certification for External System Entitlements
A common ask for Okta Identity Governance (OIG) is to be able to do access certification on external application data. Currently OIG can only run campaigns on objects (group memberships and application assignments) in the Okta Universal Directory (UD). Importing of external system entitlements is on the product roadmap. But with some understanding of the…
-
Extracting Okta ASA Audit Log with Okta Workflows
The audit logs in Okta Advanced Server Access (ASA) can be viewed in the ASA administrative interface or extracted via the ASA Audit V2 API (and this is what the integrations with SIEM tools do). But what about the situation where you just need to extract all the logs and process them somewhere? You could…
-
Inactive Application Account Reporting with Okta Workflows
I was recently asked about reporting, and possibly recertification, of inactive accounts in Okta. We can run reports in Okta on Okta profile states to find inactive users. We also have an Okta Workflows template to find and report on Okta users who haven’t accessed Okta in a period of time. But what about application…
-
Separation of Duties (SoD) With Okta Workflows
Implementation of Separation of Duties controls is often an Identity Governance requirement. Whilst SoD controls will find their way into the Okta Identity Governance product at some point, they can be implemented today using the Okta Identity Cloud data model and Okta Workflows. This article provides a sample implementation. Note that there is a later…
-
Continuous Certification with Okta Workflows
This article provides an approach to implementing continuous (re)certification using Okta Workflows. It discusses the concept and then walks through the sample implementation. IGA, Certification and Continuous Certification A key focus for Identity Governance and Administration (IGA) implementations is access certification (aka recertification or attestation). The aim of this is to periodically validate the access…
