Tag: Governance
-
OIG Access Requests – Can I Attach a File?
A common requirement for access requests is adding a file to support the request. It may not be obvious, but Okta Identity Governance has the means to attach a file to a request. Let’s explore this and show an example. How to Attach a File in the Access Requests Portal A file can be attached…
-
OIG Access Requests – Posting Questions Based on Earlier Selections
My colleague, Rajesh Kumar, showed me something today that fell into the “wow, I didn’t even think of using the product this way” category. It involves using logic in Access Request flows (Request Types) in Okta Identity Governance to prompt for additional information based on earlier selections. Let’s look at how the user experiences it,…
-
OIG Access Requests and Workflows – Checking SoD In An Access Request
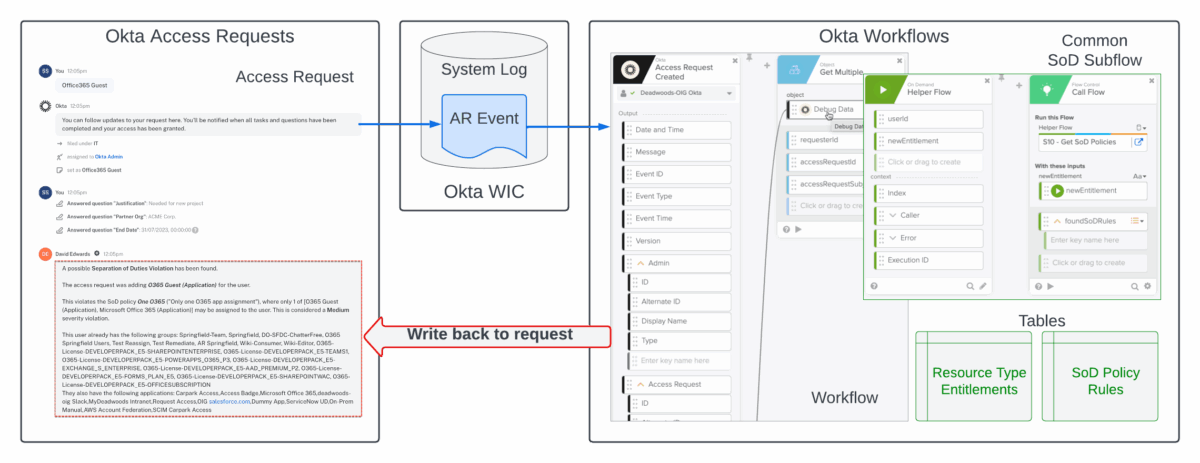
This article looks at a new approach you could use to perform Separation of Duties (SoD) checking from Okta Access Requests using Okta Workflows. It shows two approaches you could take to get SoD analysis into the request a soon as it’s raised so that the reviewer has the information at hand before approving the…
-
OIG Access Requests – Posting Additional Information into a Request
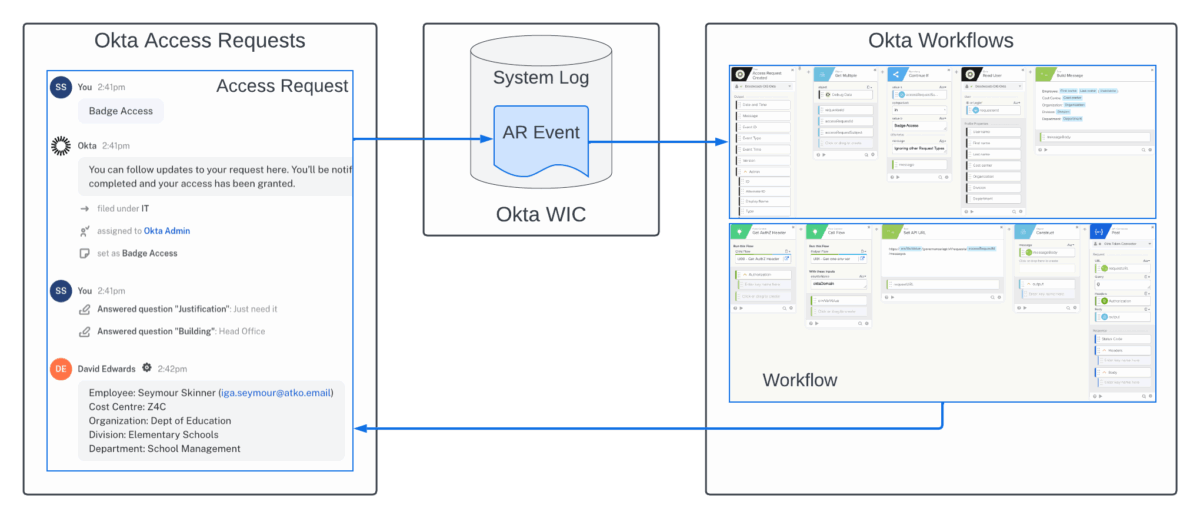
This article looks at a recent addition to the Okta Identity Governance (OIG) Access Request API that allows updating of in-flight access requests and can be used to add additional data to help reviewers review requests. Note that the OIG APIs are still in beta but can be used against preview and production Okta orgs.…
-
User Access Reviews in Okta Identity Governance
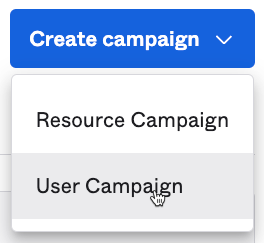
This article explores the new user campaign (User Access Review) feature in Okta Identity Governance (OIG) Access Certifications. Introduction The ability to build and run access certification campaigns against resources in Okta (groups and applications) has been in Okta Identity Governance (OIG) since it was released. In June User Campaigns was added to address User…
-
OIG Access Requests – Calling an Okta Workflow from Within a Request Type
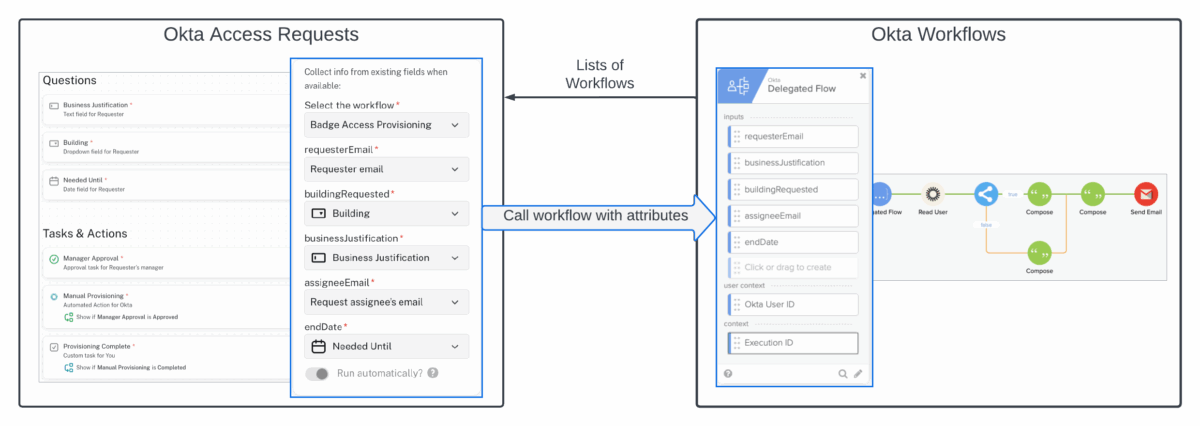
For some time there has been the ability to trigger a workflow in Okta Workflows from a request flow in Okta Access Requests via events written to the Okta System Log. Events were created for a request being initiated and being closed. But this approach has some limitations, such as a lot of processing within…
-
New Reviewer Options in OIG Access Certification
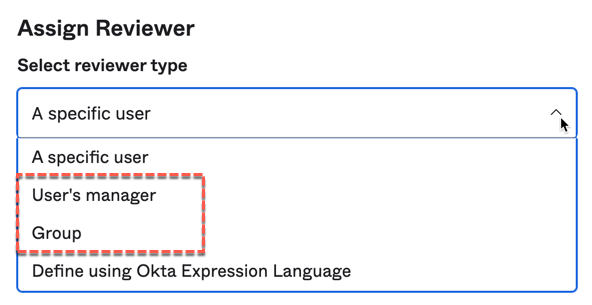
There was a recent change to the reviewer selections for Okta Identity Governance (OIG) Access Certification to allow for more options and to simplify the administrative experience. The feature is currently an Early Access feature (the “Reviewer Assignment” enhancement) that can be turned on in an OIG-enabled Okta org. It will roll into production over…
-
Okta Identity Governance and/or Service Now – Architectural Patterns
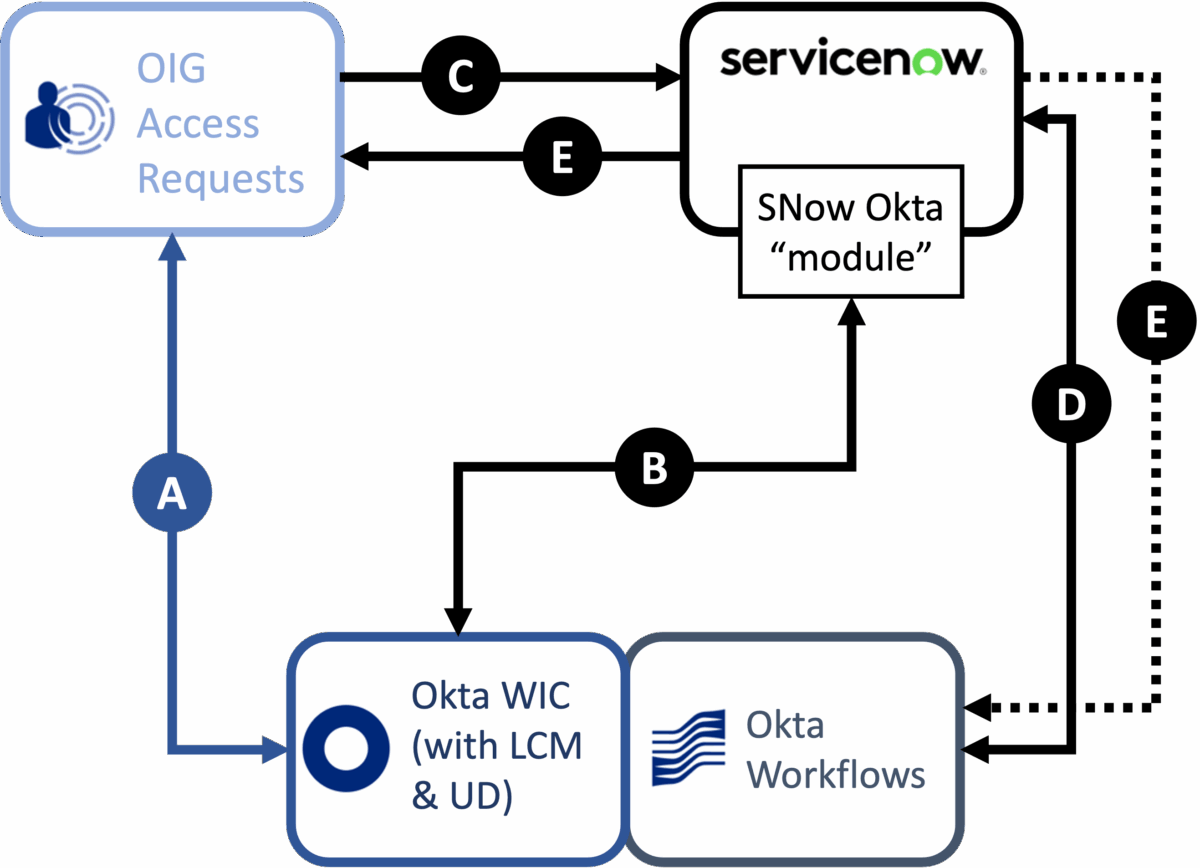
Most organisations have some ITSM or service request tool, and ServiceNow is the most common. So it’s understandable that any conversation about Okta Identity Governance, particularly access requests, will involve comparison with ServiceNow or integration patterns for both products. How do you approach an access request solution? Which product is going to meet your needs…
-
Risk-Based Application Certification in OIG
If you were at Oktane22, or have listened to the Oktane22 roadmap sessions, you will know risk and use of risk signals is a key focus for Okta going forward. This includes leveraging risk in Okta Identity Governance (OIG), to help make access requests and access certification more effective. But can you leverage risk today?…
-
Logging a ServiceNow Request via Workflows from OIG Access Requests
A common ask for Okta Identity Governance is to be able to log at ticket in a service desk tool, like ServiceNow, for manual provisioning activities after following an approval process in Access Requests. This article explores one approach to this using OIG Access Request events in the Okta System Log, Event Hooks and Okta…
-
OIG – Triggering Workflows From Access Certification Reviews
Okta Identity Governance (OIG) provides an access certification component for reviewing users and their access. When reviewing access, a reviewer (such as a users manager) can approve or revoke the access (or reassign). With the revoke action, the access certification campaign can be configured to automatically remove access or do nothing (i.e. leave the access…
-
Reassigning Managers for an Access Certification Campaign
A common requirement for Identity Governance and Administration (IGA) controls is for reassignment when a reviewer, like a manager, goes on leave. Okta Identity Governance (OIG) currently supports manual reassignment of access certification reviews by an administrator or by the reviewer themselves. But what about automatic reassignment based on a change to the user profile,…
-
Access Certification – Helping Reviewers Decide whether to Approve or Revoke Access
The user interface, and general user experience, has been a challenge with Identity Governance and Administration (IGA) products for many years. Unlike many IT products, IGA solutions are used by all business users and need an easy to use and understand interface. This is particularly so with Access Certifications – business owners (like managers or…
-
OIG Access Requests – Understanding User Grouping
Understanding user grouping mechanisms in the Okta Identity Governance (OIG) Access Requests mechanism is important to building and running access request flows. It can be confusing and this article aims to address the confusion. Note that OIG Access Requests is the old atSpoke product. The term “Okta” in this article refers to the Okta Identity…
-
OIG Access Requests – Using the New Timer Feature
This article explores the new Timer feature in Okta Identity Governance (OIG) Access Requests. It provides an overview of the new function and how it could be used for a long-term (days or weeks) access request and a short-term (hours) privileged access request. This article assumes a familiarity with the OIG Access Requests workflows. For…
-
Integrating ServiceNow with OIG Access Requests
One of the standard integration points with Okta Identity Governance (OIG) Access Requests is to log a ticket of an access request in an ITSM tool like ServiceNow. This article explores the integration between OIG Access Requests and ServiceNow. Overview of Integration The primary focus of the Okta Identity Governance (OIG) Access Requests function is…
