Tag: Access Requests
-
OIG Access Requests – Posting Additional Information into a Request
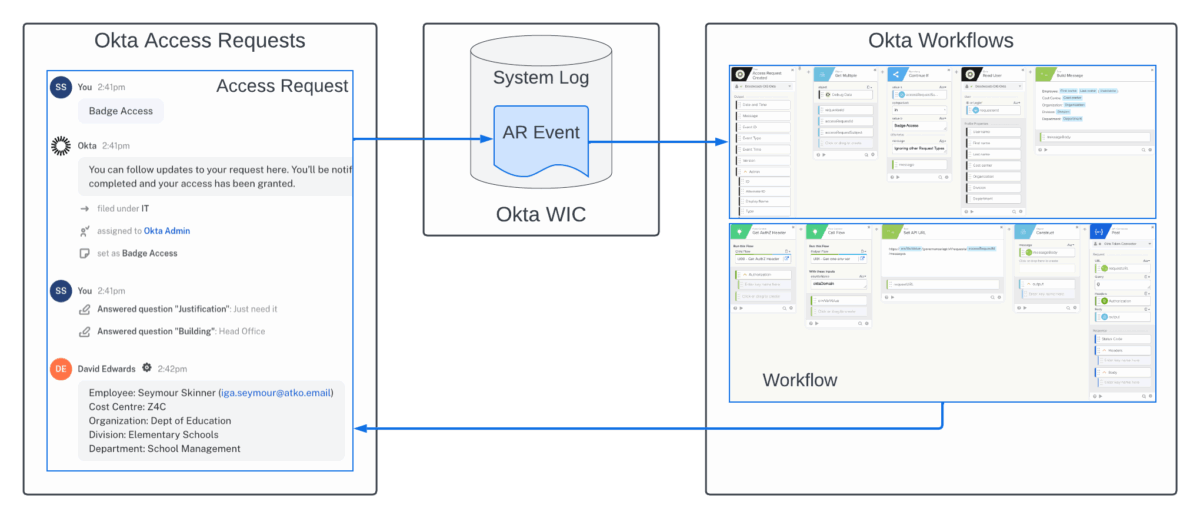
This article looks at a recent addition to the Okta Identity Governance (OIG) Access Request API that allows updating of in-flight access requests and can be used to add additional data to help reviewers review requests. Note that the OIG APIs are still in beta but can be used against preview and production Okta orgs.…
-
OIG Access Requests – Calling an Okta Workflow from Within a Request Type
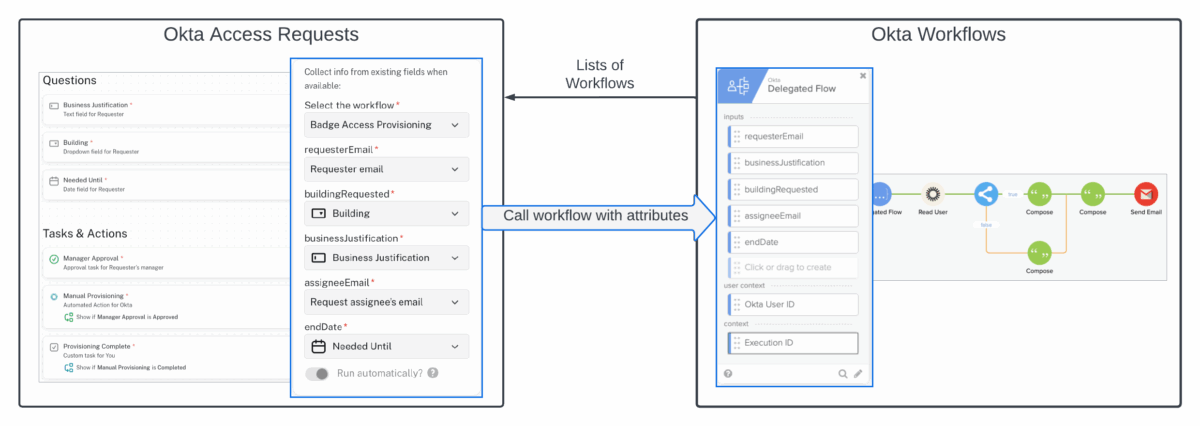
For some time there has been the ability to trigger a workflow in Okta Workflows from a request flow in Okta Access Requests via events written to the Okta System Log. Events were created for a request being initiated and being closed. But this approach has some limitations, such as a lot of processing within…
-
OIG Access Requests – Who is the Request Assignee?
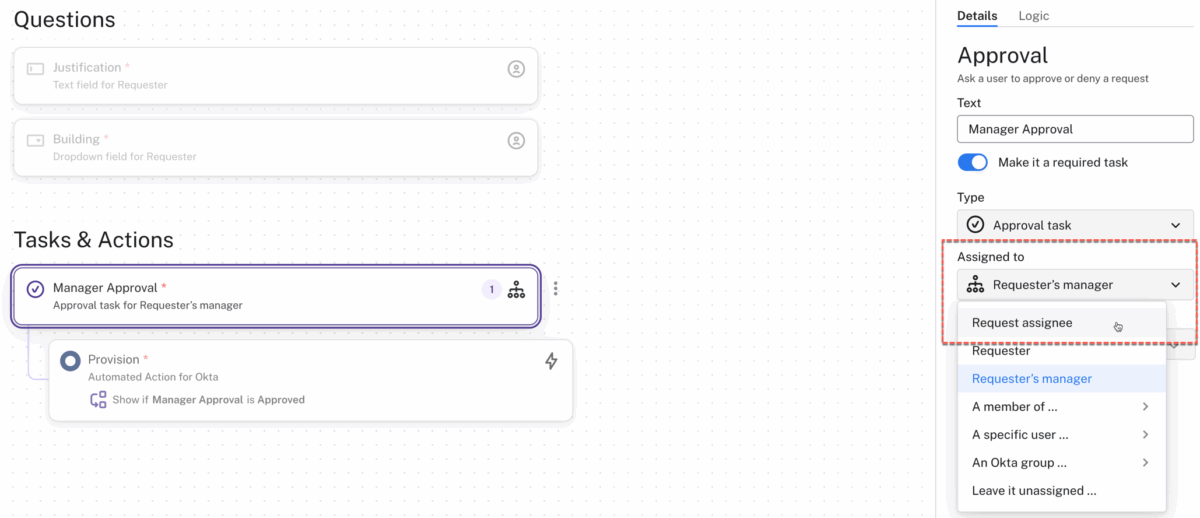
As is often the case, product documentation tells you how to turn on or configure a function but often doesn’t provide the context of that function. I found this yesterday when exploring something with a customer in Okta Identity Governance (OIG) Access Requests. What is the Request Assignee you can assign to some of the…
-
OIG Access Requests – Can an Approver Supply Information for a Request?
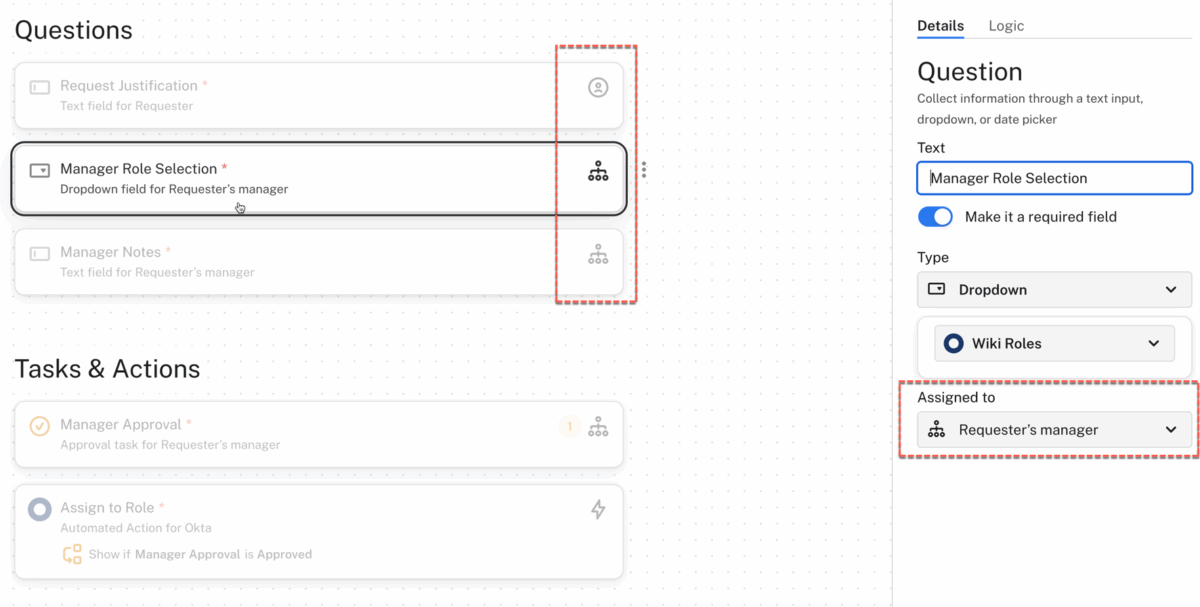
Recently someone asked if Okta Identity Governance (OIG) Access Requests could be setup so a manager could supply additional information for the request. Their use case, the requester wants access to an application but they don’t know the role they need, so the manager would select the role at the approval stage. Short answer –…
-
Did You Know the Machine Learning in OIG Access Requests Extends to the WebUI?
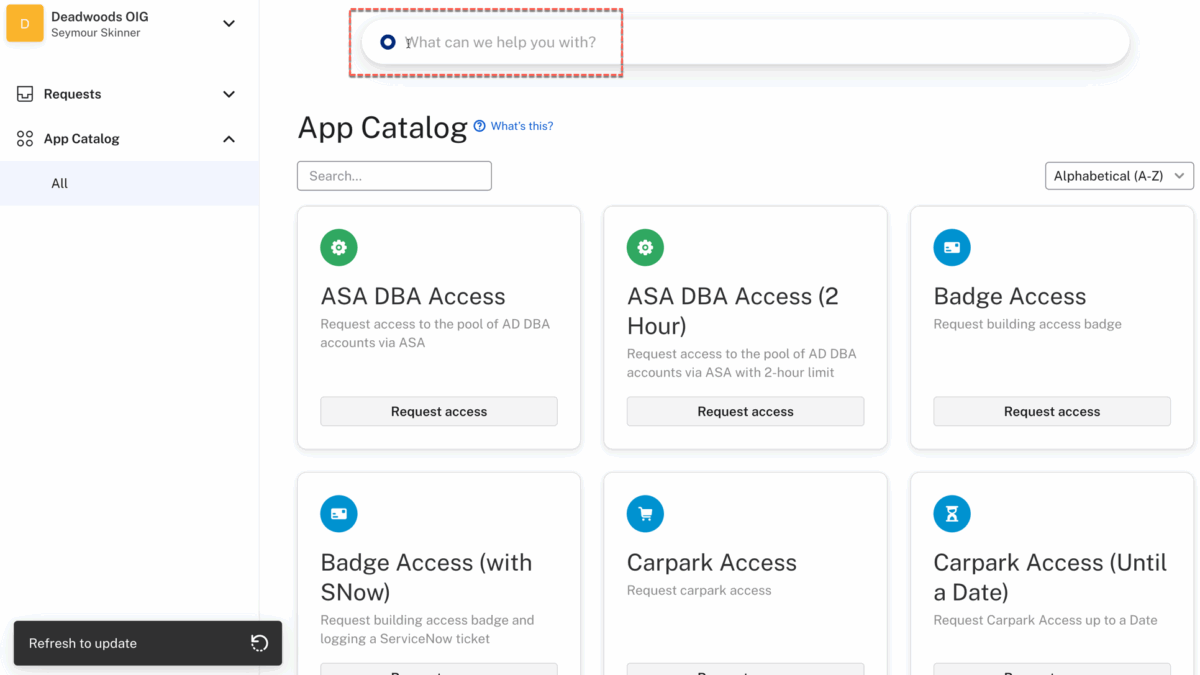
If you’ve seen a demonstration of Okta Identity Governance (OIG) Access Requests, you have probably seen the machine learning (AI) capability when requesting access in Slack or Microsoft Teams. You ask for access to something, and the AI will try to determine the best request type to present. It learns over time, so that terms…
-
Okta Identity Governance and/or Service Now – Architectural Patterns
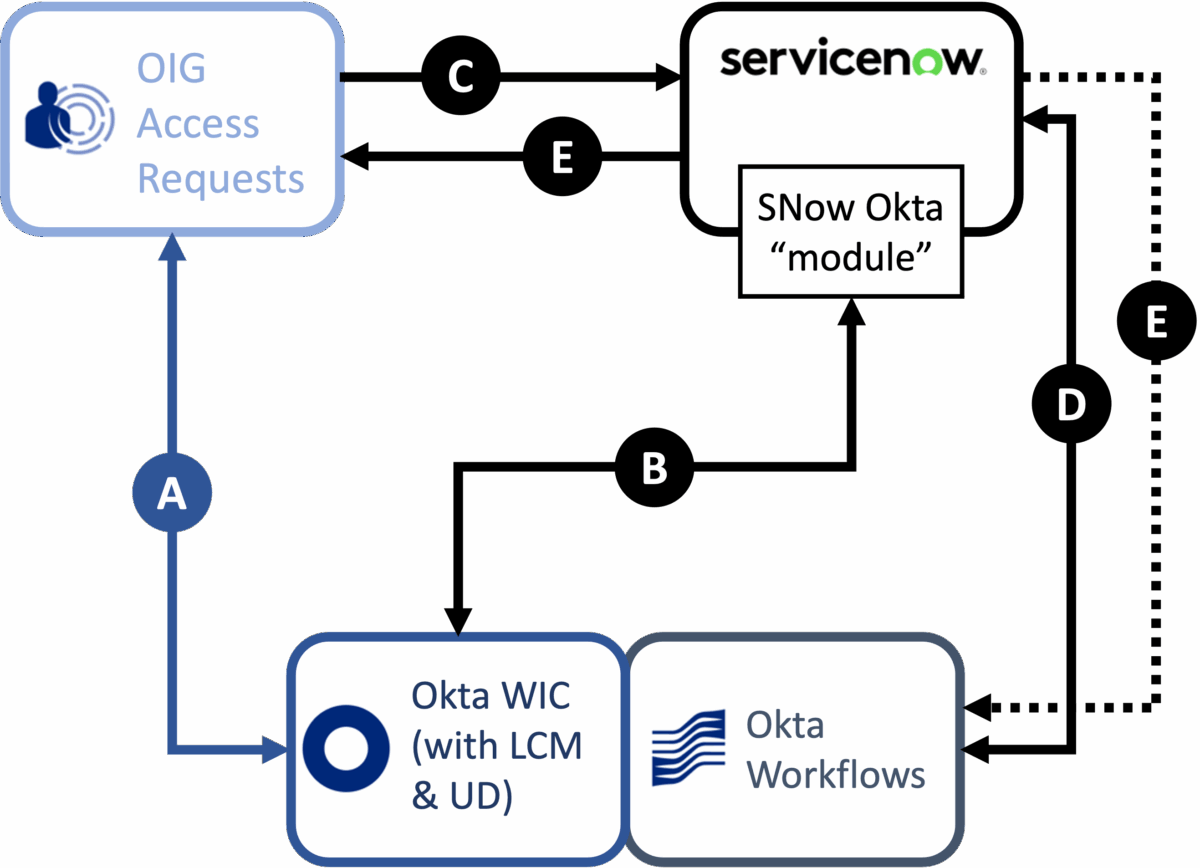
Most organisations have some ITSM or service request tool, and ServiceNow is the most common. So it’s understandable that any conversation about Okta Identity Governance, particularly access requests, will involve comparison with ServiceNow or integration patterns for both products. How do you approach an access request solution? Which product is going to meet your needs…
-
Logging a ServiceNow Request via Workflows from OIG Access Requests
A common ask for Okta Identity Governance is to be able to log at ticket in a service desk tool, like ServiceNow, for manual provisioning activities after following an approval process in Access Requests. This article explores one approach to this using OIG Access Request events in the Okta System Log, Event Hooks and Okta…
-
OIG Access Requests – Cancelling a Timer
If you’re familiar with the timer feature in Okta Identity Governance (OIG) Access Requests, you may have wondered if you can cancel a running timer and if so, how? Let’s show how it can be done. If you’re not familiar with the timer feature, have a read of this article: OIG Access Requests – Using…
-
OIG Access Requests – Clearing “Stuck” Requests
When working with Okta Identity Governance (OIG) Access Requests, you may find a request in a “stuck” state, where you can’t complete a step or the request doesn’t automatically close when done. Perhaps you’re testing a new Request Type and missed a step or have something misconfigured when you tested it. As an administrator you…
-
OIG Access Requests – Where Do I Assign Teams?
A common concern from a new Okta Identity Governance (OIG) Access Requests deployment is “I can’t see the Application or Group list when building a Request Type”. The most common cause is the assignment of Teams. Teams are the access control mechanism built into OIG Access Requests. They control who can create and own Request…
-
OIG Access Requests – Understanding User Grouping
Understanding user grouping mechanisms in the Okta Identity Governance (OIG) Access Requests mechanism is important to building and running access request flows. It can be confusing and this article aims to address the confusion. Note that OIG Access Requests is the old atSpoke product. The term “Okta” in this article refers to the Okta Identity…
-
OIG Access Requests – Using the New Timer Feature
This article explores the new Timer feature in Okta Identity Governance (OIG) Access Requests. It provides an overview of the new function and how it could be used for a long-term (days or weeks) access request and a short-term (hours) privileged access request. This article assumes a familiarity with the OIG Access Requests workflows. For…
-
Designing OIG Access Requests for Ease of Use
Access Requests are designed to be used by all people in an organisation. So making the interface and information presented be more user friendly should be a goal of any deployment. In this article we look at what information is presented to end-users by Okta Identity Governance (OIG) Access Requests and how you can use…
-
OIG Access Requests – Requesting Access in Slack
A key benefit of Okta Identity Governance is the ability to interface with access request flows via chat tools such as Slack and Microsoft Teams. This article provides a summary of the different ways users can request access in Slack and how to monitor the progress of a request in Slack. Overview of OIG Access…
-
Integrating ServiceNow with OIG Access Requests
One of the standard integration points with Okta Identity Governance (OIG) Access Requests is to log a ticket of an access request in an ITSM tool like ServiceNow. This article explores the integration between OIG Access Requests and ServiceNow. Overview of Integration The primary focus of the Okta Identity Governance (OIG) Access Requests function is…
-
Requesting Roles Through OIG Access Requests
This article looks at how Okta Identity Governance (OIG) can be used to provide a role-request feature in Access Requests. The example used is roles for Salesforce. What Roles? If you’re familiar with the Okta Identity Cloud data model, you will know there are users, groups and applications but no roles (other than roles to…
